
Government and public sector organizations are undergoing rapid digital transformation. From citizen service portals and digital identity systems to smart infrastructure and cloud-enabled collaboration, technology now underpins nearly every public function. While this modernization improves efficiency and accessibility, it also expands the cyber threat landscape and increases exposure to sophisticated attacks.
Public sector environments are inherently complex. They blend legacy infrastructure with modern cloud platforms, operate across distributed geographies, and manage highly sensitive data tied to national security, public welfare, taxation, healthcare, and law enforcement. At the same time, agencies must uphold strict compliance requirements, transparency standards, and fiscal accountability-making cybersecurity both a technical and governance priority.
Traditional, siloed security tools and manual response processes can no longer keep pace with evolving threats. Government agencies require integrated, AI-driven security platforms that provide unified visibility, intelligent detection, automated response, and compliance-ready reporting. By shifting from reactive defense to proactive resilience, public sector organizations can reduce alert fatigue, accelerate response, and safeguard the digital foundations of public trust and essential services.
Unlike private enterprises, government organizations must balance security with transparency, compliance mandates, and budget accountability. Their environments often include:
Traditional, siloed security tools struggle in such environments. Manual monitoring cannot scale. Fragmented alerts slow down response. And reactive defense models leave agencies vulnerable to persistent threats.
Public sector security requires a unified, automation-driven approach.
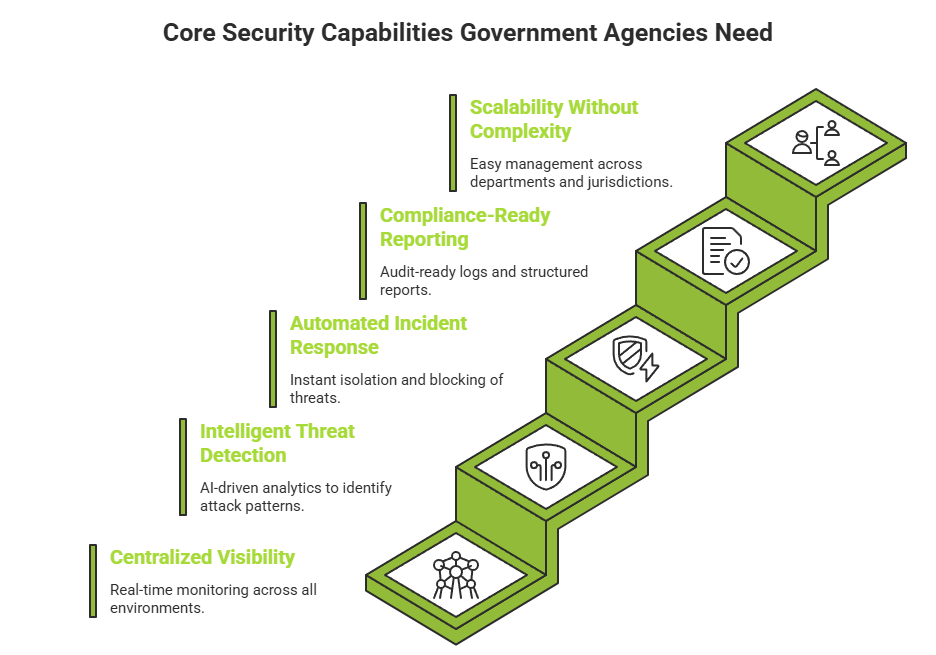
To defend national and civic digital assets effectively, public sector organizations should prioritize tools that deliver:
Government networks span on-premises systems, hybrid cloud deployments, remote offices, and mobile endpoints. Security teams need real-time visibility across the entire ecosystem-not isolated dashboards.
Unified monitoring ensures that suspicious activity in one department can be correlated with signals from another, uncovering coordinated attacks that might otherwise go unnoticed.
Signature-based detection is no longer enough. Modern threats use evasive techniques, living-off-the-land tactics, and multi-stage attack chains.
AI-driven analytics enable behavioral monitoring, anomaly detection, and contextual threat correlation. Instead of generating thousands of disconnected alerts, advanced security tools identify true attack patterns and prioritize what matters most.
In government environments, response time is critical. Delays can impact public services, compromise sensitive records, or disrupt essential infrastructure.
Automation transforms response workflows by:
This reduces dependence on manual intervention and allows security teams to act at machine speed.
Public sector entities operate under strict governance frameworks. Security tools must provide audit-ready logs, compliance dashboards, and structured reporting capabilities that align with regulatory standards.
Automated documentation not only simplifies audits but also strengthens accountability and transparency.
Government agencies range from local municipalities to national ministries. Security solutions must scale without requiring complex integrations or constant tuning.
A platform-based approach reduces tool sprawl and centralizes operations, making it easier to manage security across departments and jurisdictions.
Modern public sector cybersecurity is moving beyond fragmented tools toward integrated platforms that combine:
This convergence simplifies operations while enhancing detection accuracy and response speed. Instead of managing multiple disconnected systems, agencies gain a cohesive security architecture designed for resilience.
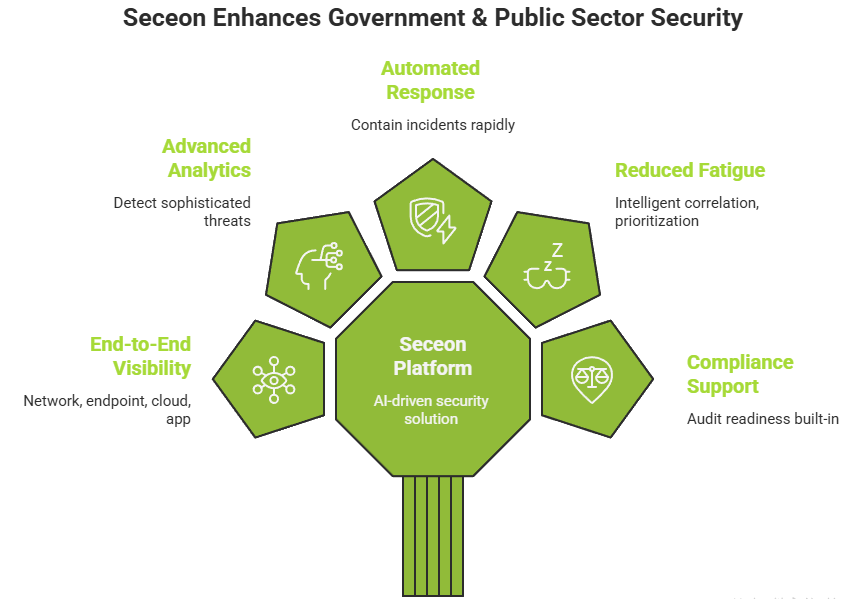
Seceon delivers a comprehensive, AI-driven security platform tailored to the operational realities of government environments. By unifying detection, analysis, and response within a single architecture, Seceon empowers agencies to move from reactive defense to proactive protection.
Key advantages include:
Rather than adding another security layer, Seceon streamlines operations while strengthening cyber resilience.
Securing Citizen-Centric Digital Transformation
Digital transformation in government is no longer optional-it is central to modern governance. From online tax filing systems and digital identity platforms to e-governance portals and smart city infrastructure, public services are increasingly delivered through connected digital ecosystems. While this transformation improves accessibility and efficiency, it also raises the stakes for cybersecurity.
Citizen data is among the most sensitive information any organization can hold. Personal identification records, financial data, healthcare information, and public safety databases must be protected not only from cybercriminals but also from state-sponsored and highly organized threat actors. A single breach can erode public confidence and disrupt essential services.
Security tools for the public sector must therefore be designed with citizen trust at the forefront. This means:
By embedding intelligent security directly into digital transformation initiatives, agencies can innovate confidently. Cybersecurity becomes an enabler of modernization rather than a barrier to it.
When governments secure their digital foundations effectively, they do more than prevent attacks-they reinforce transparency, reliability, and public trust in digital governance.
Cybersecurity in the public sector is not simply about preventing breaches-it is about safeguarding public trust. Citizens expect uninterrupted services, secure digital interactions, and responsible data stewardship.
Government security tools must therefore evolve beyond monitoring and alerting. They must anticipate threats, automate defense, and adapt continuously to emerging risks.
By embracing AI-driven, unified security platforms, public sector organizations can modernize their defense strategies, reduce operational complexity, and protect the digital foundations of governance.
In an era where cyber threats directly impact national stability and public confidence, investing in intelligent security tools is not optional-it is essential.
