
Cybersecurity has entered a phase where traditional defenses are no longer sufficient to address the scale and sophistication of modern threats. As organizations continue to expand their digital footprint adopting cloud technologies, enabling remote workforces, and integrating interconnected systems – the attack surface has grown significantly.
Today’s cyber threats are not only more frequent but also more advanced. Attackers leverage automation, artificial intelligence, and multi-stage techniques to infiltrate systems, move laterally, and remain undetected for extended periods. These attacks are often designed to bypass conventional security tools, making detection and response increasingly challenging.
In this evolving landscape, cybersecurity is no longer just about preventing attacks-it is about continuously monitoring, detecting, and responding to threats in real time. Organizations must adopt a more unified and proactive approach that provides complete visibility, faster detection, and coordinated response across all environments.
Understanding common cyber threats and the strategies to defend against them is a critical step toward building a resilient and future-ready security posture.
Cyber threats manifest in different forms, but they often share a common objective-gaining unauthorized access, disrupting operations, or extracting sensitive data.
One of the most widespread threats is social engineering, where attackers manipulate individuals into revealing confidential information. These attacks are highly effective because they exploit trust rather than technical vulnerabilities.
Ransomware has also become a major concern, evolving from simple data encryption to complex attacks involving data theft and extortion. Its impact goes beyond financial loss, often disrupting entire business operations.
At the same time, organizations face risks from within. Insider threats-whether caused by negligence or malicious intent-can lead to data exposure or system compromise due to existing access privileges.
Additionally, attackers frequently use malware and advanced techniques to establish long-term access within systems. These threats operate silently, making them difficult to detect using traditional security tools.
Cloud environments introduce another layer of risk. Misconfigurations in cloud infrastructure can unintentionally expose sensitive data, often without immediate visibility.
Traditional cybersecurity tools are often designed to operate in isolation, focusing on specific areas such as endpoints or networks. While effective to a certain extent, they lack the ability to provide a complete picture of the threat landscape.
This fragmented approach creates visibility gaps, making it difficult to detect complex, multi-stage attacks. Security teams may receive multiple alerts from different tools without the context needed to understand the full scope of an incident.
As cyber threats continue to evolve, organizations need a unified approach that connects data across all layers and enables faster, more accurate decision-making.
Defending against modern cyber threats requires a combination of visibility, intelligence, and rapid response. Rather than relying on isolated tools, organizations must adopt a more integrated and proactive strategy.
A strong defense framework typically includes:
These measures work together to create a layered defense that can adapt to evolving threats.
One of the biggest challenges in cybersecurity is the lack of visibility across the entire IT environment. Without a unified view, it becomes difficult to identify how an attack starts, spreads, and impacts different systems.
Real-time detection plays a critical role in addressing this challenge. By continuously analyzing system behavior and correlating data from multiple sources, organizations can identify threats as they emerge rather than after the damage is done.
This shift from reactive to proactive detection significantly reduces response time and limits the impact of attacks.
Detection alone is not enough-organizations must also be able to respond quickly and effectively. Delayed responses can allow attackers to move laterally, escalate privileges, and expand their reach within the system.
Modern cybersecurity strategies emphasize automation and streamlined response processes. This includes isolating affected systems, blocking malicious activity, and preventing further spread-all in real time.
An efficient response capability ensures that threats are contained before they escalate into major incidents.
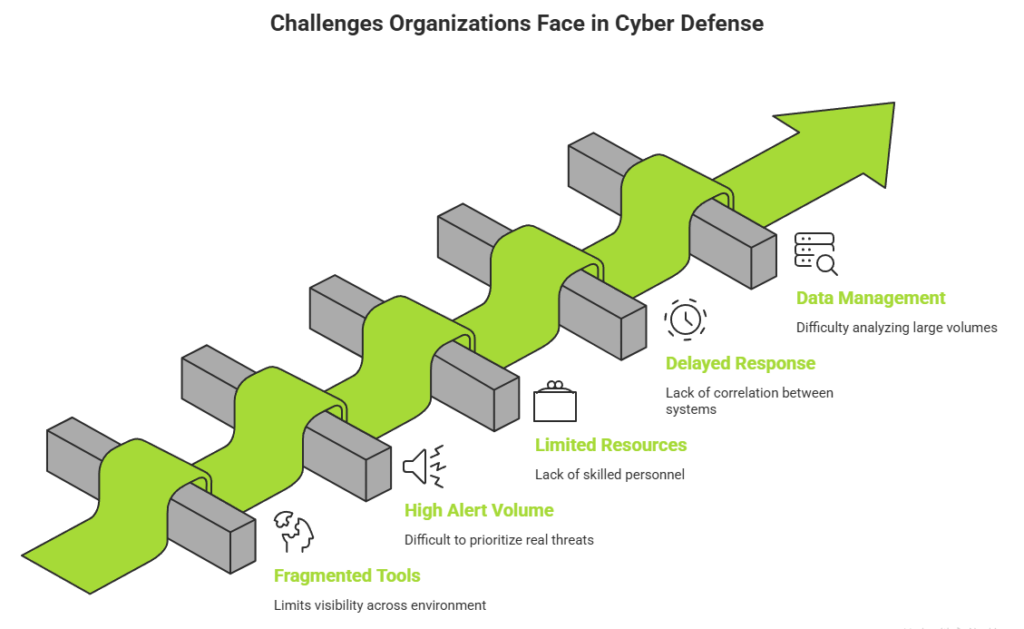
Despite advancements in security technologies, many organizations struggle to maintain effective protection. The complexity of modern IT environments, combined with the increasing volume of threats, creates several operational and strategic challenges.
Some of the most common challenges include:
These challenges often lead to inefficiencies, missed threats, and increased risk. Addressing them requires a more integrated and intelligent approach to cybersecurity that simplifies operations while improving visibility and response capabilities.
To stay ahead of modern threats, organizations must move toward a unified security model. This approach integrates detection, analysis, and response into a single framework, providing complete visibility and control.
A proactive strategy focuses on identifying risks early, understanding attack patterns, and responding in real time. It also reduces reliance on manual processes by leveraging automation and advanced analytics.
By aligning security operations across all environments, organizations can improve efficiency, reduce risk, and strengthen their overall defense posture.
Seceon provides a unified platform designed to deliver intelligent and automated cybersecurity monitoring across the entire enterprise environment.
The platform integrates advanced analytics, behavioral intelligence, and real-time threat detection to help organizations gain deep visibility into security activity across networks, endpoints, identities, and cloud infrastructure.
Key capabilities include:
Comprehensive Data Visibility
Seceon continuously collects and analyzes telemetry across diverse IT environments, ensuring security teams have a complete and accurate view of activity across their infrastructure.
AI-Powered Threat Detection
Advanced analytics and machine learning models identify anomalies, suspicious behavior, and emerging threats in real time, enabling faster and more accurate detection.
Contextual Event Correlation
Security data from multiple sources is automatically correlated to uncover complex attack patterns and provide meaningful context for investigation.
Automated Alert Prioritization
The platform filters noise and highlights the most critical security events, allowing teams to focus on high-impact incidents without being overwhelmed.
Streamlined Incident Response
With integrated automation and contextual insights, organizations can respond to threats more quickly and effectively, reducing overall impact.
By bringing these capabilities together into a unified platform, Seceon enables organizations to continuously monitor their environments, detect threats earlier, and respond with greater efficiency.

Cyber threats today are dynamic, persistent, and constantly evolving. As organizations expand their digital environments, the need for a more adaptive and intelligent approach to cybersecurity becomes increasingly important.
Traditional, fragmented security measures are no longer sufficient. Modern strategies must focus on continuous visibility, real-time detection, and coordinated response across all layers. This enables organizations to identify threats earlier and respond with greater speed and accuracy.
Cybersecurity is not just a technical function-it is a strategic priority. By combining the right technologies with strong processes and awareness, organizations can strengthen their defenses and reduce risk.
Ultimately, those that embrace a proactive and unified approach will be better positioned to stay ahead of evolving threats and ensure long-term resilience.
