
Modern organizations operate in highly dynamic digital environments that span cloud infrastructure, remote workforces, SaaS applications, and interconnected enterprise systems. While these technologies accelerate business growth, they also significantly expand the attack surface. Cyber adversaries are becoming more sophisticated, leveraging stealth techniques, automated tools, and multi-stage attack strategies that often evade traditional security defenses.In this evolving threat landscape, relying solely on reactive security measures is no longer sufficient. Security teams must adopt a proactive approach that continuously searches for hidden threats while ensuring that incidents are contained and remediated quickly. This is where a Threat Hunting and Incident Response Platform becomes critical to maintaining a strong security posture.
Threat hunting is the proactive process of identifying malicious activities that bypass traditional detection systems. Instead of waiting for alerts triggered by predefined signatures or rules, security teams actively analyze network behavior, endpoint activity, user behavior patterns, and system anomalies to uncover potential threats.
Modern threat hunting relies heavily on advanced analytics, machine learning, and behavioral detection models. By analyzing vast amounts of telemetry data across the enterprise, security platforms can identify suspicious patterns that indicate compromise attempts, lateral movement, credential abuse, or data exfiltration.
However, manual threat hunting alone is resource-intensive and difficult to scale. Organizations require intelligent platforms capable of automating data correlation, anomaly detection, and investigative workflows while enabling security analysts to validate findings quickly.
Effective threat hunting is not a random process. It follows structured methodologies that allow security teams to systematically uncover hidden threats within enterprise environments.
In this approach, security analysts begin with a hypothesis based on known attacker techniques, threat intelligence reports, or unusual system behaviors. For example, analysts may investigate abnormal authentication patterns or unusual data transfer activities that could indicate credential misuse or data exfiltration attempts.
Indicator-based hunting focuses on identifying known indicators of compromise (IOCs) such as malicious IP addresses, suspicious domains, or known malware signatures. Security teams use these indicators to search across enterprise telemetry to determine whether the organization has been exposed to a known threat.
Advanced threat actors often use techniques that leave minimal signatures. Behavioral threat hunting focuses on identifying anomalies in user behavior, endpoint activity, and network traffic. By analyzing deviations from normal patterns, security teams can uncover stealthy attacks that traditional detection systems may miss.

Detecting threats is only the first step in cybersecurity defense. Once suspicious activity is identified, organizations must respond rapidly to contain the attack before it spreads across systems or compromises sensitive data.
Incident response involves a structured set of processes designed to identify, analyze, contain, eradicate, and recover from security incidents. In modern environments where attacks unfold within minutes, manual response processes can significantly delay containment efforts.
An integrated Threat Hunting and Incident Response Platform enables security teams to move seamlessly from detection to remediation. By combining threat intelligence, automated investigation capabilities, and response orchestration, such platforms significantly reduce the time required to contain security incidents.
This integration ensures that security teams are not only detecting threats faster but also responding to them with precision and efficiency.
A comprehensive platform designed for modern security operations should deliver multiple capabilities that work together to provide visibility, intelligence, and automated response.
Advanced platforms continuously monitor network traffic, endpoint activity, user behavior, and application interactions to identify anomalies that may indicate malicious activity. Behavioral analytics helps detect sophisticated threats that do not match known signatures.
Security data often comes from multiple sources including firewalls, endpoints, cloud platforms, identity systems, and network devices. A robust platform correlates telemetry from these sources in real time to identify multi-stage attacks and complex threat patterns.
Machine learning models and advanced analytics can identify indicators of compromise, suspicious behaviors, and attack techniques. Automated detection reduces the burden on security teams while improving detection accuracy.
Modern platforms provide built-in hunting frameworks that allow analysts to search for indicators of compromise across large datasets. These frameworks enable analysts to investigate suspicious activity efficiently without manually parsing massive logs.
Once a potential threat is detected, analysts require contextual visibility to understand the attack scope. Incident investigation capabilities provide timelines, attack chains, entity relationships, and behavioral insights that help security teams quickly determine the severity of an incident.
To minimize damage, platforms should support automated response actions such as isolating compromised endpoints, blocking malicious IP addresses, terminating suspicious processes, or revoking compromised credentials. Automation accelerates containment while reducing manual workload.
Integrating global threat intelligence helps security platforms identify known malicious indicators and emerging attack campaigns. This intelligence enhances detection accuracy and provides additional context for incident investigations.
One of the major challenges faced by security teams today is the sheer volume of alerts generated by security tools. Manual investigation of every alert can significantly slow down response times.
Automation plays a critical role in improving incident response efficiency by:
• Automatically correlating events across multiple security systems
• Prioritizing high-risk alerts using advanced analytics
• Triggering predefined containment actions when malicious activity is confirmed
• Reducing manual investigation time for security analysts
By automating repetitive tasks and orchestrating response workflows, security platforms enable security teams to focus on complex threat investigations rather than routine operational tasks.
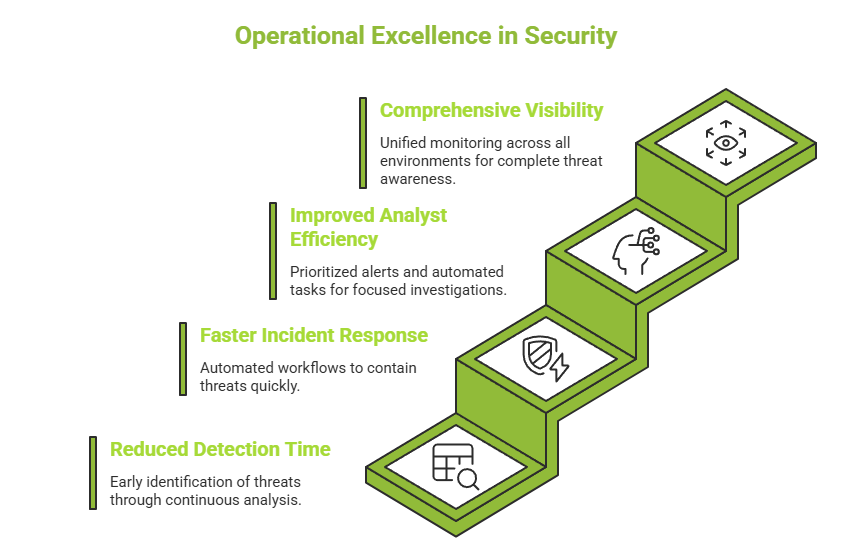
Implementing a threat hunting and incident response platform provides several operational advantages for modern security teams.
By continuously analyzing behavioral data and correlating telemetry across systems, security platforms can identify threats much earlier in the attack lifecycle.
Automated investigation workflows and response actions dramatically reduce the time required to contain threats, minimizing potential damage.
Security teams often face alert fatigue due to overwhelming volumes of security notifications. Intelligent platforms prioritize high-risk alerts and automate repetitive tasks, allowing analysts to focus on strategic investigations.
Unified monitoring across networks, endpoints, users, and cloud environments ensures that security teams have complete visibility into potential threats across the organization.
Organizations investing in threat hunting and incident response capabilities must continuously measure operational performance to improve detection and response effectiveness. Security metrics provide valuable insights into how efficiently threats are being identified and contained.
This metric measures how quickly a security team can identify a potential threat after it enters the environment. Lower detection times indicate stronger monitoring and threat hunting capabilities.
MTTR measures the time required to contain and remediate a detected incident. Efficient response workflows and automation significantly reduce this metric.
Security teams often handle thousands of alerts daily. Platforms that reduce false positives and provide contextual insights allow analysts to investigate alerts more effectively and prioritize high-risk threats.
Organizations should assess how well their security platform monitors endpoints, networks, cloud environments, and identity systems to ensure comprehensive threat coverage.
Many organizations rely on multiple disconnected security tools to manage threat detection and response. While each tool may provide specific capabilities, this fragmented approach creates several operational challenges.
Security teams often struggle with limited visibility across environments, slow investigations due to manual data correlation, and delayed response times caused by fragmented workflows. Additionally, analysts may experience alert fatigue when multiple tools generate uncoordinated alerts.
A unified platform that combines threat detection, threat hunting, and incident response capabilities eliminates these challenges by providing centralized visibility, automated correlation, and streamlined response processes.
How Seceon Enhances Threat Hunting and Incident Response
Seceon’s platform is designed to support modern security operations through intelligent automation, behavioral analytics, and unified threat visibility. By continuously analyzing security telemetry across the enterprise, the platform identifies suspicious behaviors and potential attack patterns in real time.
Seceon enables proactive threat hunting through advanced analytics that surface hidden threats often missed by traditional security tools. Security teams can investigate incidents through contextual insights, attack timelines, and correlated event data that simplify complex investigations.
By combining advanced analytics, automated threat detection, and integrated response capabilities, Seceon enables security teams to shift from reactive alert handling to proactive threat management. The platform continuously analyzes security telemetry across endpoints, networks, identities, and cloud environments to identify complex attack patterns that may otherwise remain undetected.
In addition to detection and investigation, Seceon accelerates incident response by automating containment actions and remediation workflows. This integrated approach enables organizations to detect threats earlier, respond faster, and reduce the operational burden on security teams.
As cyber threats continue to evolve, organizations must shift from reactive defense strategies to proactive security operations. Threat hunting combined with automated incident response is becoming a foundational capability for modern security teams.
Platforms that integrate continuous monitoring, intelligent detection, and automated response provide organizations with the agility needed to combat sophisticated threats. By empowering security teams with advanced analytics and automation, organizations can significantly strengthen their cybersecurity posture.A unified Threat Hunting and Incident Response Platform ensures that threats are not only detected quickly but also contained before they can impact critical systems and data. For organizations seeking to enhance their security operations, adopting such a platform is no longer optional-it is essential.
