
Cybersecurity in 2026 is no longer defined by the absence of tools-it is defined by the challenge of choosing the right ones and making them work together effectively.
As organizations expand across cloud environments, remote workforces, and interconnected systems, security operations have become increasingly complex. Threats are no longer isolated incidents. They unfold across multiple layers, often moving silently between endpoints, identities, and networks before being detected.
In response, organizations have adopted a range of technologies to strengthen their defenses. Among the most prominent are XDR, SIEM, and SOAR. Each represents a different approach to solving core security challenges, yet the growing overlap between them has made decision-making more complicated.
The question organizations face today is not simply which technology to adopt, but how to align these capabilities into a strategy that delivers real security outcomes.
The debate around XDR, SIEM, and SOAR is rooted in the evolution of security operations.
SIEM emerged to centralize visibility, giving organizations a way to collect and analyze data from across their infrastructure. As environments grew more complex, the volume of data increased, and with it, the number of alerts.
This led to operational challenges. Security teams found themselves spending more time managing alerts than investigating actual threats. In response, SOAR was introduced to bring efficiency to operations by automating repetitive tasks and standardizing response processes.
However, even with automation, a critical issue remained-the lack of context. Alerts often lacked the depth needed to understand whether they were part of a larger attack.
This gap led to the rise of XDR, which focuses on correlating data across multiple layers to provide a clearer, more complete picture of threats.
The coexistence of these technologies has created confusion, but it also reflects a deeper shift in how cybersecurity is being approached.
SIEM continues to serve as a foundational component of many security strategies. It provides centralized data collection and supports compliance, auditing, and long-term analysis.
In large and complex environments, this role remains essential. Organizations need a reliable way to retain and analyze historical data, especially for regulatory and investigative purposes.
At the same time, the limitations of SIEM have become more evident. The sheer volume of data it processes can generate an overwhelming number of alerts, many of which require manual analysis. Without deeper context, distinguishing between noise and real threats becomes increasingly difficult.
As a result, SIEM is no longer seen as a complete solution for modern threat detection, but rather as one part of a broader security architecture.
As security teams faced increasing pressure to respond faster, SOAR introduced a new level of operational efficiency.
By automating workflows and orchestrating actions across multiple tools, SOAR reduces the burden on analysts and ensures more consistent incident handling. It allows organizations to move from manual response processes to more structured and repeatable actions.
However, SOAR’s effectiveness is closely tied to the quality of the data it receives. It does not generate insights on its own but depends on upstream systems to provide accurate and meaningful alerts.
This means that while SOAR improves response speed, it does not address the challenge of detecting and understanding threats at a deeper level.
XDR represents a shift toward more integrated and context-driven security.
Instead of analyzing events in isolation, XDR brings together data from across the environment and correlates it in real time. This approach allows organizations to identify patterns and relationships that would otherwise remain hidden.
In practice, this leads to fewer alerts, but with significantly higher relevance. Security teams gain a clearer understanding of ongoing threats, enabling faster and more informed decision-making.
XDR is not just an additional tool-it reflects a broader change in how detection is approached. It emphasizes context, correlation, and real-time visibility across systems.
The ongoing comparison between XDR, SIEM, and SOAR often leads to the assumption that one can replace the others. In reality, they address different aspects of the same operational challenge.
SIEM focuses on visibility and data management.
SOAR focuses on execution and response efficiency.
XDR focuses on detection and contextual understanding.
The real challenge is not choosing one over the other, but determining how these capabilities should be combined based on organizational needs.
Security strategies in 2026 are increasingly defined by how well these elements are aligned. Organizations that treat them as isolated solutions often struggle with inefficiencies, while those that integrate them effectively are better positioned to detect and respond to threats.
The right cybersecurity strategy today is not built around a single technology. It is built around outcomes-faster detection, clearer insights, and more effective response.
For some organizations, the priority may be improving visibility and maintaining compliance. For others, it may be reducing response times or gaining better context into complex threats.
Understanding these priorities is essential in determining how XDR, SIEM, and SOAR should be positioned within the security architecture.
What is becoming increasingly clear is that modern security operations require a balance of all three capabilities. Detection without context leads to noise. Automation without intelligence leads to risk. Visibility without action limits effectiveness.
Cybersecurity in 2026 is moving toward more unified and integrated models. Organizations are seeking to reduce fragmentation by bringing detection, analysis, and response closer together.
This shift is driven by the need for speed and accuracy. As threats become more sophisticated, the ability to act quickly and decisively becomes a critical advantage.
Integrated approaches allow security teams to move seamlessly from detection to response, reducing delays and improving overall efficiency. They also simplify operations by minimizing the need to manage multiple disconnected tools.
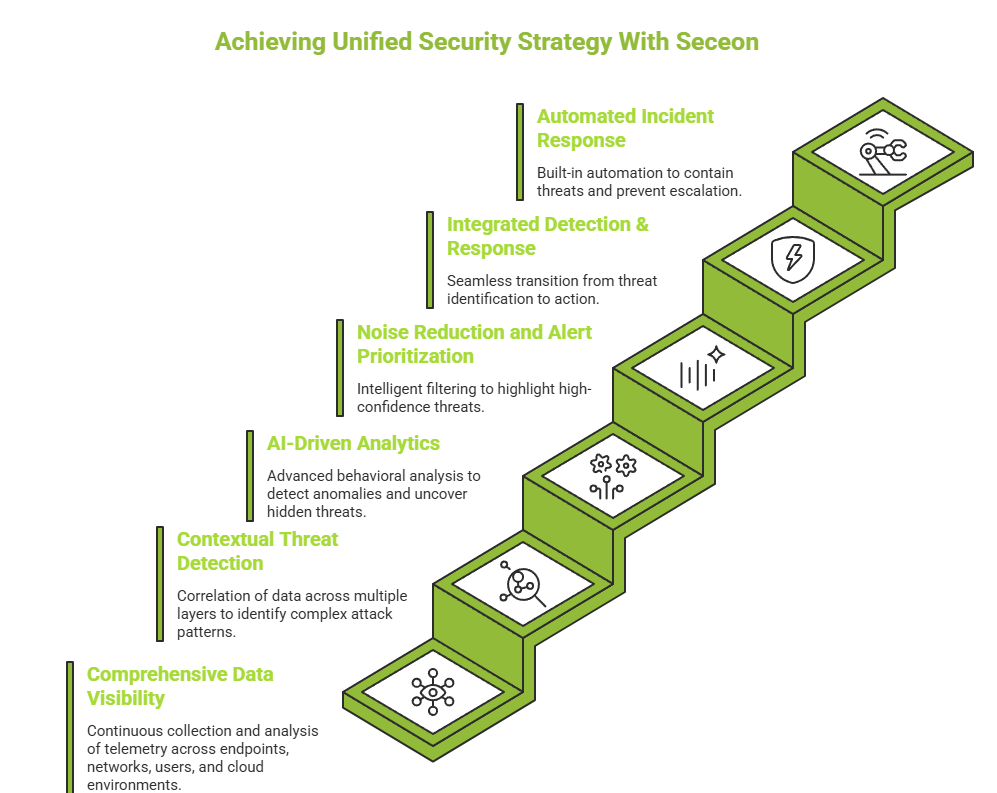
Enabling a Unified Strategy with Seceon
As organizations work to align XDR, SIEM, and SOAR capabilities into a cohesive security strategy, one of the biggest challenges they face is integration. Managing multiple tools, correlating data across systems, and ensuring timely response often introduces complexity that slows down operations instead of improving them.
Seceon addresses this challenge by bringing together the core capabilities associated with modern security operations into a single, unified platform-connecting visibility, detection, and response in a seamless manner.
Key capabilities include:
By combining these capabilities within a single framework, Seceon enables organizations to simplify their security operations while improving detection accuracy and response speed-aligning closely with the evolving demands of cybersecurity in 2026.
The conversation around XDR, SIEM, and SOAR is often framed as a choice, but in reality, it reflects a broader shift in how cybersecurity strategies are being designed.
Each plays a distinct role. SIEM continues to provide the foundation for visibility and governance. SOAR brings consistency and speed to response operations. XDR adds the context and intelligence required to detect modern, multi-stage threats.
The right strategy in 2026 is not about selecting one over the others-it is about aligning these capabilities to work as a cohesive system. When visibility, detection, and response are connected, security operations become more effective, adaptive, and resilient.
As threat environments continue to evolve, organizations that focus on integration over fragmentation will be better positioned to reduce complexity, accelerate decision-making, and respond to threats with greater precision and confidence. This approach allows organizations to reduce operational complexity while strengthening their ability to detect and respond to modern threats with greater speed and accuracy..
