In an era of escalating cyber threats and tightening regulatory scrutiny, cybersecurity compliance monitoring has become one of the most critical functions in enterprise security. Yet for many organizations, it remains reactive, fragmented, and manual – a costly gap that regulators and adversaries alike are quick to exploit.
This guide provides a comprehensive look at what cybersecurity compliance monitoring is, why it matters, how it works, the frameworks that govern it, and the best practices organizations should follow to build a program that scales with their risk and regulatory exposure.
Cybersecurity compliance monitoring is the ongoing process of measuring, validating, and enforcing security controls against applicable laws, regulations, and internal policies. Unlike a one-time audit, it is a continuous discipline – one that provides real-time or near-real-time assurance that an organization’s security posture aligns with its obligations.
It operates across several interconnected functions:
Policy enforcement visibility: Confirming that security policies – covering access controls, encryption, patching schedules, and data handling – are actively enforced at all times, not just documented.
Regulatory control mapping: Aligning security telemetry and audit logs to the specific requirements of applicable compliance frameworks.
Configuration drift detection: Identifying deviations from approved security baselines across endpoints, cloud workloads, network devices, and applications before they become audit findings or attack surfaces.
Evidence collection: Automatically capturing and preserving the forensic records needed to demonstrate compliance to auditors, regulators, and cyber insurance underwriters.
Real-time alerting on control failures: Notifying the right teams the moment a compliance control breaks down, rather than weeks later during a scheduled review.
The goal is not compliance for its own sake – it is to ensure that the security controls an organization claims to have are actually working, continuously, and that evidence of this can be produced on demand.
The stakes around compliance have risen substantially in recent years, driven by three converging pressures: regulatory expansion, rising breach costs, and growing board-level accountability.
Governments and industry bodies around the world are issuing more prescriptive cybersecurity regulations with shorter compliance windows and steeper penalties for non-compliance. The EU’s DORA regulation introduced mandatory ICT risk management and third-party oversight requirements. The SEC now requires public companies to disclose material cybersecurity incidents within four business days. State-level privacy laws are multiplying across the United States, each with its own breach notification timelines and data protection standards.
Organizations that fail to maintain continuous compliance evidence face not just fines, but the inability to demonstrate reasonable care – a key factor in litigation, insurance claims, and regulatory enforcement actions.
The financial consequences of compliance failures extend well beyond regulatory penalties. The global average cost of a data breach reached $4.88 million in 2024, with organizations that lacked mature compliance programs suffering losses significantly higher than industry peers. Beyond direct costs, non-compliance drives up cyber insurance premiums, creates barriers to enterprise contracts, and damages the customer trust that underpins long-term revenue.
In most jurisdictions, cybersecurity is no longer solely a technical concern – it is a governance obligation. Directors and senior executives can now face personal liability for compliance failures. This has driven demand for compliance posture visibility at the board level, requiring security teams to translate technical control status into executive-ready reporting on a continuous basis.
Most organizations do not operate under a single regulatory framework. They face a mosaic of overlapping requirements, each with distinct control mandates, audit timelines, and evidence standards. Understanding the major frameworks is essential for designing a compliance monitoring architecture that satisfies all of them efficiently.
• PCI DSS v4.0: Governs the protection of cardholder data in payment environments. Requires continuous monitoring of network segmentation, access controls, vulnerability management, and logging across all systems that store, process, or transmit payment card data.
• HIPAA / HITECH: Mandates technical, physical, and administrative safeguards for protected health information (PHI). Requires audit controls, access management, transmission security, and breach notification readiness across all covered entities and business associates.
• NIST Cybersecurity Framework (CSF) 2.0: A widely adopted voluntary framework covering six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. Increasingly referenced in regulatory expectations and contractual requirements across sectors.
• DORA (Digital Operational Resilience Act): Applies to financial entities and their ICT service providers operating in the EU. Requires robust ICT risk management, incident reporting, operational resilience testing, and third-party risk oversight.
• NIS2 Directive: The EU’s expanded network and information security directive, covering critical infrastructure sectors. Requires incident reporting within 24 hours, supply chain risk management, and board accountability for cybersecurity.
• SOC 2 Type II: A trust-based reporting standard covering Security, Availability, Processing Integrity, Confidentiality, and Privacy. Requires continuous evidence capture across control environments over audit periods of 6-12 months.
• ISO 27001: An international information security management standard requiring a formal ISMS, risk assessment methodology, and ongoing monitoring and improvement of security controls.
• GDPR / CCPA and State Privacy Laws: Data protection regulations requiring lawful basis for processing, breach notification within mandated timeframes, and demonstrable data governance controls. Over 23 US states now have active privacy laws with varying requirements.
The compliance burden is compounded by the overlap between these frameworks. Many organizations must satisfy five or more simultaneously, with differing evidence requirements, audit schedules, and remediation timelines. A compliance monitoring program built on manual processes and siloed tools cannot sustain this.
Despite its importance, most organizations struggle to maintain effective compliance monitoring programs. Several structural challenges make this difficult:
Modern security environments generate hundreds of millions of events daily. Security teams inundated with false positives frequently miss the genuine control failures that compliance auditors will identify – and that threat actors will exploit. Without intelligent filtering and prioritization, compliance monitoring becomes an exercise in noise management rather than risk reduction.
Annual or quarterly compliance assessments capture a snapshot of the security environment at a single moment. Configuration drift, access control changes, and policy violations that occur between assessment cycles remain invisible until the next audit – or until a breach forces discovery. Continuous monitoring is the only effective response to this structural gap.
Organizations running dozens of disparate security products – separate SIEM, SOAR, EDR, NDR, vulnerability management, and identity tools – struggle to correlate compliance-relevant data across these silos. The result is incomplete audit trails, inconsistent control documentation, and evidence gaps that create risk during regulatory examinations.
Compliance reports assembled manually from multiple systems introduce transcription errors, framework inconsistencies, and preparation delays. In sectors with short incident notification windows – four days for SEC disclosures, 72 hours for GDPR breaches, 24 hours for NIS2 major incidents – slow manual processes are not just inefficient; they are a compliance risk in themselves.
The global cybersecurity workforce gap continues to widen. Organizations are being asked to do more compliance work with fewer qualified personnel. This makes automation not a luxury but a operational necessity – particularly for small and mid-size enterprises that lack the headcount of large enterprise security teams.
Organizations seeking to build or mature a compliance monitoring program should approach it as an architectural discipline, not a point-in-time project. The following principles provide a foundation for programs that are both effective and sustainable.
Establish a unified data foundation first: Effective compliance monitoring requires comprehensive, correlated visibility. Consolidating security telemetry into a single platform before attempting framework mapping eliminates the evidence gaps that fragmented tools create. A unified data foundation is the prerequisite for everything else.
Monitor continuously, not periodically: Replace scheduled compliance assessments with continuous monitoring that tracks the real-time state of security controls. Compliance posture should be a live dashboard, not a quarterly report.
Map controls to frameworks automatically: Build or leverage pre-built mappings between security events and regulatory control requirements. Manual control mapping consumes disproportionate analyst time and introduces inconsistency. Automated mapping ensures that every relevant event is attributed to the correct compliance obligations in real time.
Define remediation SLAs by control criticality: Not all compliance gaps carry equal risk. A failed MFA control on a privileged account requires a different response timeline than a minor configuration deviation on a low-risk system. Establish tiered remediation SLAs and automate enforcement.
Maintain continuous audit readiness: Audit-ready evidence should be collected and organized continuously, not assembled in the weeks before an audit window opens. Organizations that treat audit readiness as a project rather than an operating state consistently perform worse in regulatory examinations.
Integrate compliance into security operations: Compliance monitoring and security operations should not be separate functions. When a threat detection event implicates a compliance control, the response workflow must address both dimensions simultaneously. Siloed compliance teams that operate independently of the SOC create structural blind spots.
Automate evidence collection and reporting: Compliance reports should be generated automatically from continuous monitoring data, not assembled manually. Automated reporting reduces errors, accelerates audit response times, and frees security staff to focus on risk reduction rather than documentation.
Account for third-party and supply chain risk: Most compliance frameworks now require oversight of third-party service providers and supply chain partners. Compliance monitoring programs must extend beyond the organization’s own environment to include visibility into third-party risk posture.
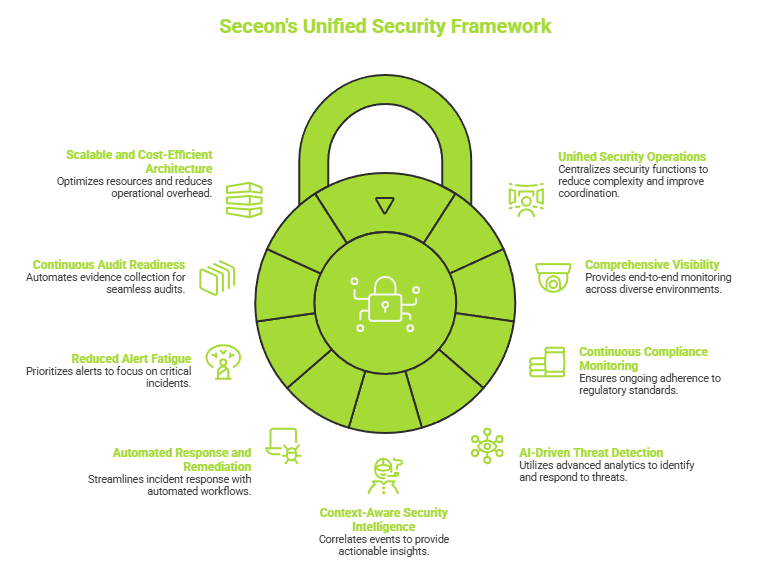
Modern organizations require more than standalone security tools – they need a unified, intelligent approach that can simplify operations, strengthen visibility, and improve response efficiency across increasingly complex environments.
Seceon helps organizations address the operational and compliance challenges of modern cybersecurity through an AI-driven platform designed to unify security monitoring, threat detection, automated response, and compliance visibility within a single operational framework.
Unified Security Operations
Brings together multiple security functions into a centralized platform, helping reduce operational complexity, eliminate tool sprawl, and improve coordination across security teams.
Comprehensive Visibility Across the Environment
Provides end-to-end visibility across endpoints, networks, cloud infrastructure, identity systems, SaaS applications, and OT/IoT environments to reduce blind spots and improve monitoring coverage.
Continuous Compliance Monitoring
Helps organizations continuously monitor security controls, detect policy violations, configuration drift, and access anomalies, while supporting alignment with major regulatory frameworks and industry standards.
AI-Driven Threat Detection and Analytics
Uses advanced analytics, behavioral modeling, and AI-driven correlation to identify suspicious activity, emerging threats, and anomalous behavior with greater speed and accuracy.
Context-Aware Security Intelligence
Correlates events and telemetry across the environment to provide actionable context, helping security teams prioritize high-risk incidents and accelerate investigations.
Automated Response and Remediation
Supports automated workflows for threat containment, incident response, evidence collection, and remediation activities, helping reduce manual effort and improve operational efficiency.
Reduced Alert Fatigue
Applies intelligent prioritization and contextual analysis to reduce unnecessary alerts and help analysts focus on the incidents that present the greatest business and compliance risk.
Continuous Audit Readiness
Automates evidence collection, audit trail maintenance, and reporting processes to help organizations maintain ongoing compliance visibility and streamline audit preparation.
Scalable and Cost-Efficient Architecture
Simplifies security and compliance operations through a unified platform approach that helps optimize resources, improve SOC efficiency, and reduce overall operational overhead.
By combining visibility, automation, analytics, and compliance monitoring into a single platform, Seceon helps organizations move from fragmented and reactive security operations toward a more proactive, resilient, and continuously monitored cybersecurity posture.
Cybersecurity compliance monitoring is no longer a back-office function or a periodic audit exercise. It is a core operational discipline that sits at the intersection of security, governance, and business risk management. The organizations that treat it as such – investing in continuous monitoring, automated evidence collection, and integrated compliance operations – are better positioned to withstand both regulatory scrutiny and adversarial pressure.
The regulatory landscape will continue to evolve. New frameworks will emerge, existing ones will be updated, and the evidence standards auditors apply will become more demanding. Organizations that build their compliance monitoring programs on manual processes and fragmented tools will find themselves perpetually playing catch-up. Those that invest in continuous, automated, AI-driven compliance infrastructure will find that compliance becomes a sustainable operational baseline rather than a recurring crisis.
