
Cyber threats are evolving faster than most organizations can respond. Modern enterprises face an increasingly complex threat landscape driven by ransomware, nation-state attacks, insider threats, cloud misconfigurations, supply chain risks, and AI-assisted cybercrime. At the same time, security teams are challenged by fragmented tools, alert fatigue, staffing shortages, and rapidly expanding attack surfaces.
Traditional security approaches – built around isolated point products and manual investigation workflows – are no longer sufficient for detecting and responding to threats at the speed required by today’s environments. Organizations need the ability to continuously monitor activity, correlate threats across multiple domains, and respond quickly before incidents escalate into major breaches.
This is where Threat Detection and Response (TDR) platforms have become essential. Modern TDR platforms help organizations improve visibility, accelerate threat detection, automate response actions, and strengthen overall security operations through a more centralized and intelligent approach to cyber defense.
A Threat Detection and Response (TDR) platform is an integrated cybersecurity solution designed to identify, investigate, prioritize, and respond to cyber threats across an organization’s infrastructure.
Rather than functioning as a standalone security tool, a TDR platform acts as a centralized operational layer that combines visibility, analytics, automation, and response orchestration across the enterprise.
Modern TDR platforms typically ingest and correlate telemetry from:
The goal is not simply to generate alerts – it is to transform raw security telemetry into actionable intelligence that enables rapid and effective incident response.
Core functions of a threat detection and response platform include:
A modern TDR platform enables organizations to move beyond reactive security operations toward continuous and proactive cyber defense.
Cyberattacks today are faster, stealthier, and more coordinated than ever before. Adversaries increasingly exploit identity systems, cloud infrastructure, remote work environments, and third-party supply chains to bypass traditional perimeter defenses.
Attackers are also leveraging automation and AI-driven techniques to accelerate reconnaissance, phishing, privilege escalation, and lateral movement.
Organizations relying solely on legacy security tools often lack the visibility and correlation capabilities needed to detect these attacks early in the kill chain.
Modern enterprise environments generate enormous volumes of security events every day. Security analysts frequently face thousands of alerts across disconnected systems, many of which are false positives or low-priority events.
Without intelligent correlation and prioritization, security teams struggle to distinguish critical threats from operational noise. This leads to delayed investigations, missed indicators of compromise, and increased analyst burnout.
Threat detection and response platforms help reduce this burden by applying contextual analytics, behavioral modeling, and automation to identify the incidents that matter most.
Today’s organizations operate across on-premises infrastructure, public cloud environments, SaaS applications, remote endpoints, and distributed networks. This creates fragmented visibility and inconsistent security operations.
Threat detection and response platforms provide centralized monitoring and cross-domain correlation that help organizations maintain visibility across increasingly distributed environments.
The longer a threat remains undetected, the greater the operational, financial, and reputational impact.
Modern ransomware campaigns can encrypt critical systems within hours. Data exfiltration, privilege escalation, and lateral movement often occur long before traditional investigations begin.
Rapid detection and automated response capabilities help organizations reduce dwell time, contain threats faster, and minimize operational disruption.
Despite increased cybersecurity investment, many organizations continue to struggle with operational inefficiencies that limit threat detection and response effectiveness.
Many security teams operate dozens of disconnected tools across SIEM, EDR, SOAR, NDR, vulnerability management, identity security, and cloud monitoring.
This fragmentation creates visibility gaps, duplicated workflows, and operational complexity.
High alert volumes overwhelm analysts and increase the likelihood of missed threats.
Without intelligent prioritization and automation, SOC teams spend excessive time investigating low-value events.
The cybersecurity skills shortage continues to impact organizations globally. Many teams lack the staffing required to support 24/7 monitoring and rapid incident response.
Automation and AI-driven workflows are becoming essential operational requirements rather than optional enhancements.
Manual investigations across multiple consoles and datasets significantly increase response times.
Disconnected workflows make it difficult to establish attack timelines and understand the full scope of compromise.
Hybrid infrastructure, cloud adoption, remote work, and third-party integrations create monitoring blind spots that attackers increasingly exploit.
Organizations require unified monitoring strategies that extend across the full attack surface.
Modern organizations require more than isolated security products – they need a unified, intelligent platform capable of simplifying operations, improving visibility, and accelerating response across increasingly complex environments.
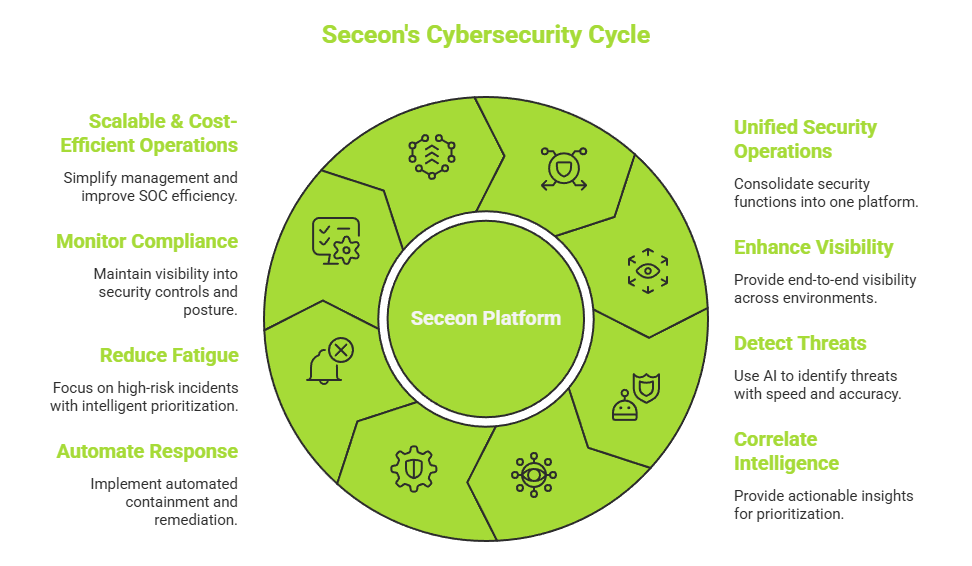
Seceon helps organizations strengthen threat detection and response through an AI-driven platform designed to unify security monitoring, analytics, automated response, and compliance visibility within a centralized operational framework.
Unified Security Operations
Consolidates multiple security functions into a single platform, helping organizations reduce tool sprawl, simplify workflows, and improve operational efficiency.
Comprehensive Visibility Across Hybrid Environments
Provides end-to-end visibility across endpoints, networks, cloud infrastructure, identity systems, SaaS applications, and OT/IoT environments.
AI-Driven Threat Detection
Uses advanced analytics, behavioral modeling, and AI-driven correlation to identify known and unknown threats with greater speed and accuracy.
Contextual Threat Intelligence
Correlates events across the environment to provide actionable insights that help analysts prioritize incidents and accelerate investigations.
Automated Threat Response
Supports automated containment, remediation, and response workflows that reduce response times and improve operational consistency.
Reduced Alert Fatigue
Applies intelligent prioritization and contextual analysis to help security teams focus on the highest-risk incidents.
Continuous Compliance Monitoring
Helps organizations maintain visibility into security controls, audit readiness, and compliance posture across multiple frameworks.
Scalable and Cost-Efficient Operations
Simplifies security management through a unified architecture designed to improve SOC efficiency while reducing operational overhead.
By combining detection, analytics, automation, and compliance visibility into a single platform, Seceon helps organizations move from reactive security operations toward a more proactive and resilient cybersecurity strategy.
Threat detection and response is no longer just a SOC function – it is a foundational requirement for modern enterprise resilience.
As attack surfaces continue to expand and cyber threats become more sophisticated, organizations must move beyond fragmented tools and reactive security models. Continuous visibility, AI-driven analytics, automated response, and integrated operations are becoming essential components of effective cybersecurity programs.
Organizations that modernize their detection and response capabilities are better positioned to reduce breach impact, improve operational efficiency, strengthen compliance readiness, and respond to evolving threats with greater speed and confidence.
The question is no longer whether organizations need advanced threat detection and response capabilities – it is whether their current security operations model can keep pace with the realities of today’s threat landscape.
